Introduction
A very common configuration for SMBs, particularly those running Microsoft Small Business Server, is to throw all the Exchange services on one box, forward ports 25, 80, and 443 to it, plug in your MX records, and call it a day. However, any experienced messaging administrator will tell you that it's a security concern to have your mailboxes sitting on the same server that has a publicly accessible SMTP service. Basically, you are inviting anyone and everyone to come put files on your server. Couple this with the fact that many businesses are running their servers with no messaging security component, such as Trend Micro's "Worry-Free Business Security Advanced" or Microsoft's Forefront for Exchange, and you have a recipe for quickly piling up unwanted mail, or worse.
Although a large enterprise might normally setup an edge server in a DMZ to receive mail, that's not a realistic option for the small business. So, in swoops a service such as AppRiver to save the day, providing you affordable hosted messaging security by acting as the middle-man for incoming (and usually outgoing) mail between you and the rest of the internet. Problem solved, right? Wrong. Normal, RFC-abiding mail servers may send all your mail to the secure hosted system you specified in those MX records starting with the lowest number, but not the wise spammer. He'll find port 25 open on your network and start spamming away, completely bypassing the filter. Here's how to avoid that and ensure your Exchange server only communicates with your filtering service.
Step 1: Lockdown Receive Connector
Fire up your Exchange console and drill down to Server Configuration > Hub Transport. You should already have one "Internet" connector there. Although Microsoft recommends you simply change this one, I like to leave it in place as a quick way to "re-enable" inbound mail from all sources should you ever need to.
Start by creating a new Receive Connector (Action > Server > New Receive Connector ...). Give it a logical name and specify that this will be a "Custom" connector. You should be able to keep the defaults where they are unless this is a multi-homed server and you only wish to receive mail on one interface. Don't forget to set your HELO response banner to the external FQDN (e.g. mail.domain.tld). This would also be a good time to mention that proper PTR and MX records are important.
Now that you have your connector in place, right-click on it and let's change the properties. First, you'll want to remove the entry for 0.0.0.0-255.255.255.255 in the "Receive mail from these IP addresses" box. Enter all of the IP addresses provided by your hosted filtering service (AppRiver's can be found here).
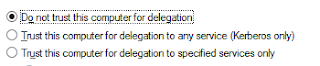
Leave all the authentication mechanisms off and what we have is an external connector that will only listen to mail coming from AppRiver. Now you can disable your internet connector and test the configuraion.
Step 2: Lockdown Send Connector
Outbound filtering is a great feature that most hosted filtering providers offer. Sometimes this feature has to be requested, but it will help prevent your users from forwarding spam or sending viruses to other networks.
Create a new Send Connector (Action > New Send Connector). Assign a name and use the "Custom" option for the type of connector.
Add a new SMTP address space, using an asterisk (*) for the address. This will tell Exchange to use this connector for all destinations. In the network settings, select the option to "Route mail through the following smart hosts". Use the FQDN or IP of the smart host you were given by your filtering provider (server###.appriver.com, for example) after clicking "Add".
Your provider will tell you if they require authentication (AppRiver does not), which will need to be specified in the "Configure smart host authentication settings" screen. After your send connector is setup, just disable the existing Internet connector and enable your new custom connector.
Of course, you can do all of this from the command line in EMS if you like. If you are curious about those commands, you can view the shell command output from any of these actions when looking at the completion screen in EMC.








No comments:
Post a Comment