UPDATE: Turns out this is a known issue during the 1.5 > 5.1 VSM upgrade and a fix should be released in an upcoming patch.
That's about the shortest title I could think of to be descriptive of this issue. TLDR is that NAT rules on vShield Edge appliances appear to be causing unexpected behavior on VPN traffic
after a vCloud upgrade from 1.5 to 5.1.
Background: We recently upgraded from 1.5 to 5.1. For most of our vDCs, we simply have a
single vSE/Routed network that connects a private subnet to a "WAN" network and
pulls a public IP from a pool. We forward (NAT) and allow (firewall) selected
ports (e.g. 3389 for RDP) to virtual machines. Most of these networks also have
a site-to-site VPN tunnel with a physical firewall across the internet. After
the upgrade, we went and converted our rules to match on original IP and then
enabled "multiple interfaces" - effectively taking them out of compatibility
mode. Everything looked good (even for the vSE devices still in compatibility
mode)
Issue: We first noticed this when a client reported that
they could not access a virtual machine via RDP using it's internal (VSE
protected) IP across a VPN tunnel, but could access the VM via RDP using it's
public hostname/IP address. We allow all traffic across the VPN (firewall has an
any:any rule for VPN traffic). When we logged in to troubleshoot (simply
thinking the VPN was down), we found that we could connect to any port on the
remote VM across the VPN tunnel
except 3389. I could ping from the
local subnet to the troubled VM on the vApp network with no problem. I could
connect to other ports that were open on the remote VM with no problem. I could
not connect to 3389 across the VPN.
We thought it might be isolated, but found the issue on every VSE we have: If
there existed a DNAT rule to translate inbound traffic for a particular port,
that port would be unresponsive when traffic traversed the VPN tunnel destined
for the target of the DNAT rule.
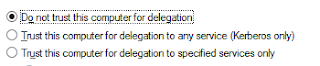
While vCloud Director doesn't show anything strange in the firewall section of vSE configuration, if you log in to vShield Manager and look at the firewall rules there, a "Deny"
rule with the
private/internal/translated IP is added for any NAT rule
that exists:
This, I'm assuming, is for security
reasons during the upgrade but it does not show up in vCloud Director (thus our
confusion). After taking our appliances out of compatibility mode post-upgrade,
the rules were still there.
Solution: After the vSE is out of compatibility mode (see pg. 49 of the
vCD 5.1 Install Guide), re-apply the service configuration (Right-Click vShield Edge Appliance in vCloud Director and select "Re-Apply Service Configuration"). You can also re-deploy the appliance or add an arbitrary rule to the firewall list - both appear to have the same effect.



Everything looked good (even for the anonymous vSE devices still in compatibility mode)
ReplyDeleteVPN is offered to remote workplaces and individual clients with the goal that they can get to the system of the association in a successful way.buy vpn online
ReplyDeleteGreat Information sharing .. I am very happy to read this article .. thanks for giving us go through info.Fantastic nice. I appreciate this post. private internet access review
ReplyDeleteThe tips said in this article ought to have the capacity to enable you to pick the best VPN supplier. It is perfect to have a rundown of a couple of VPN suppliers. To pick the best specialist organization, you have to consider every one of the tips specified above while evaluating the shortlisted specialist organizations.VPN service
ReplyDeleteWhile free VPN services are good, the amount of security that they offer is questionable and you are only provided with a small list of servers to choose from. Moreover, the features of the VPN service are also limited.utorrent
ReplyDeleteWhat is VPN? VPN is a shortened form for virtual private system. It can be characterized as the strategy that is generally connected to add to the protection and the security into people in general and private systems, the web and Wi-Fi hotspots. read
ReplyDeleteHow effective the VPN server is will significantly affect the speed.india vpn proxy
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteAlso,https://novavpn.com/blog/yify/ running your VPN straightforwardly on a quicker CPU PC brings down the association time and consequently making your VPN speed to be speedier, than running the VPN on a switch.
ReplyDeletePersons appreciate shopping for amazing, appealing, fascinating and from time to time attractive aromas for them selves and pertaining to others. This can be executed conveniently along with inexpensively in an on-line perfume shop. diebestenvpn
ReplyDeleteWaow this is quite pleasant article, my sister love to read such type of post, I am going to tell her and bookmarking this webpage. Thanks https://prywatnoscwsieci.pl
ReplyDeleteThank you again for all the knowledge you distribute,Good post. I was very interested in the article, it's quite inspiring I should admit. I like visiting you site since I always come across interesting articles like this one.Great Job, I greatly appreciate that.Do Keep sharing! Regards, diadiktiokaiasfalia
ReplyDeleteSo luck to come across your excellent blog. Your blog brings me a great deal of fun.. Good luck with the site. lemigliorivpn
ReplyDeleteCorporates utilize it to impart in secrecy video, voice or information over an open system.https://www.router-reset.com/does-avast-vpn-keep-logs/
ReplyDeleteFor other helpful tips & tricks, or to submit your own question to be answered, visit my site at, http://whatsmyrouterip.com/.
ReplyDeleteI've been contemplating composing an extremely tantamount post in the course of the last couple of weeks, I'll most likely keep it straightforward and connection to this rather if thats cool. Much obliged vpnveteran.com
ReplyDeleteThis blog has communicated its importance in a short yet clear way, so compact.
ReplyDeletebest VPN service
It is likewise a decent choice when workers are dissipated everywhere throughout the globe. VPN for privacy
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteWow, this is really interesting reading. I am glad I found this and got to read it. Great job on this content. I like it. https://allertaprivacy.it
ReplyDeleteI recently came across your article and have been reading along. I want to express my admiration of your writing skill and ability to make readers read from the beginning to the end. I would like to read newer posts and to share my thoughts with you. deze website
ReplyDeleteThe primary server is divided to work as free VPS. This gives you sole responsibility for space and gives you a limitation free server condition. This article examines four manners by which VPS improves your presentation and upgrades your business. cheap
ReplyDeleteIPSec - Developed by the Internet Engineering Task Force, to get trades of information at the IP layer. It is generally utilized for making VPNs free pc vpn
ReplyDeleteThe area name framework (DNS) is the way that Web space names are found and converted into IP addresses and is needed for perusing the Web. best free vpn for streaming movies
ReplyDeleteI’m going to read this. I’ll be sure to come back. thanks for sharing. and also This article gives the light in which we can observe the reality. this is very nice one and gives indepth information. thanks for this nice article... https://www.sorrisieservizi.it/internet/vpn-sicura-e-gratuita/
ReplyDeleteThanks for an interesting blog. What else may I get that sort of info written in such a perfect approach? I have an undertaking that I am just now operating on, and I have been on the lookout for such info. แทงหวยออนไลน์
ReplyDeleteCheck your availability by pinging a few Internet destinations. On the off chance that that doesn't work, ping the loopback address 127.0.0.1. On the off chance that that falls flat, your connector may not be working or it isn't as expected arranged.https://onohosting.com/
ReplyDeleteI think this is an informative post and it is very beneficial and knowledgeable. Therefore, I would like to thank you for the endeavors that you have made in writing this article. All the content is absolutely well-researched. Thanks... หวยยี่กี
ReplyDeleteNumerous VPNs will not simply support your telephone; you'll likewise have the option to ensure your PC, PC association and whatever other gadgets that interface with the web. This article traces all that you need to think about Android VPNs. best vpn reddit
ReplyDeleteThe advantage is that it gives the security that the organization on which it is based can't give. It utilizes the web to move information. Many such organizations can be made by utilizing various frameworks joining encryption and other security components to guarantee that main approved clients can get to the organization and data can't be caught by the others. anchor
ReplyDeleteAt the point when one intends to purchase a private intermediary, he can most likely track down an incredible number of ways. my sources
ReplyDeleteThanks for taking the time to discuss this, I feel strongly about it and love learning more on this topic. If possible, as you gain expertise, would you mind updating your blog with extra information? It is extremely helpful for me. debestevpn
ReplyDeleteGreat survey, I'm sure you're getting a great response. mejoresvpn
ReplyDeleteOne more said "One of my instructors utilized Skype. That is up close and personal collaboration. Assuming I generally disapproved of some numerical statement I was chipping away at, I could snap a photo of it and placed it on the Skype screen. She could see where I was committing my error. Concise Finance Wandsworth UK Retirement Mortgage
ReplyDeleteThe advantage is that it gives the security that the organization on which it is based can't give. It utilizes the web to move information. Many such organizations can be made by utilizing various frameworks fusing encryption and other security components to guarantee that main approved clients can get to the organization and data can't be caught by the others. It resembles a passage worked to send information between an organization of say an association and a far off client. It conceals your information and IP address. cheap web hosting services
ReplyDeleteI’ve been searching for some decent stuff on the subject and haven't had any luck up until this point, You just got a new biggest fan!.. ExpressVPN Discount
ReplyDeleteBusinesses nowadays have come about global market and logistics. Companies are apt for fast, secure and reliable communications. During the growth of internet, businesses are frequently extending their own networks. dark web links
ReplyDeleteGetting the top VPN company for you is always going to be something you need to think about carefully because this is something that will be needed for you if you are using the internet every day. This will especially be something that has to be thought as being very important when you use your computer to send private business or work information through to another server or co-worker; the amount of cyber attacks that happens today in the business world are huge and it is not rival companies trying to find out what are your next moves but in... work from home jobs
ReplyDelete
ReplyDeleteFun + Freebies? Yes please! TikTok Purple Ticket gives out real summer swag. Invite 2+ friends and claim your chance to win a speaker, tumbler, and more!
https://vm.tiktok.com/ZShhFpBuy/
Live meeting translation is an AI-driven solution that translates conversations during conferences, calls, or virtual sessions in real time. With live meeting translation, spoken dialogue is captured, processed, and delivered as translated text or audio almost instantly. This ensures that participants speaking different languages can understand each other without interruption. Live meeting translation supports multiple languages and adapts to various accents and speech speeds. It is highly useful for international teams, webinars, and business collaborations. By using live meeting translation, organizations can create more inclusive and productive communication environments.
ReplyDeleteAn ai language translator uses advanced algorithms to convert text and speech into different languages. With an ai language translator, users can achieve accurate and fast results. These tools support real-time translation and multiple languages. An ai language translator is useful for business, travel, and education. By using an ai language translator, users can communicate effectively across cultures. These platforms also provide voice and text options. An ai language translator improves productivity and saves time. Overall, an ai language translator is essential for modern multilingual communication.
ReplyDeleteBoost your online visibility with a professional directory submission service designed to help startups and businesses grow faster. StartupSubmit offers a reliable directory submission service that manually lists your website across 250+ high-authority platforms, improving SEO performance, domain authority, and organic traffic. Unlike automated tools, this directory submission service uses real human submissions to ensure quality backlinks and higher acceptance rates. It is ideal for founders looking to gain early traction, increase brand exposure, and rank higher on search engines and AI platforms. Choose this directory submission service to build credibility, drive targeted traffic, and achieve long-term digital growth.
ReplyDelete